Salience’s xASM platform
Explore advanced cybersecurity solution with Salience's xASM platform: an extended solution for internal, external, and API security analysis.
- 14-day money-back guarantee
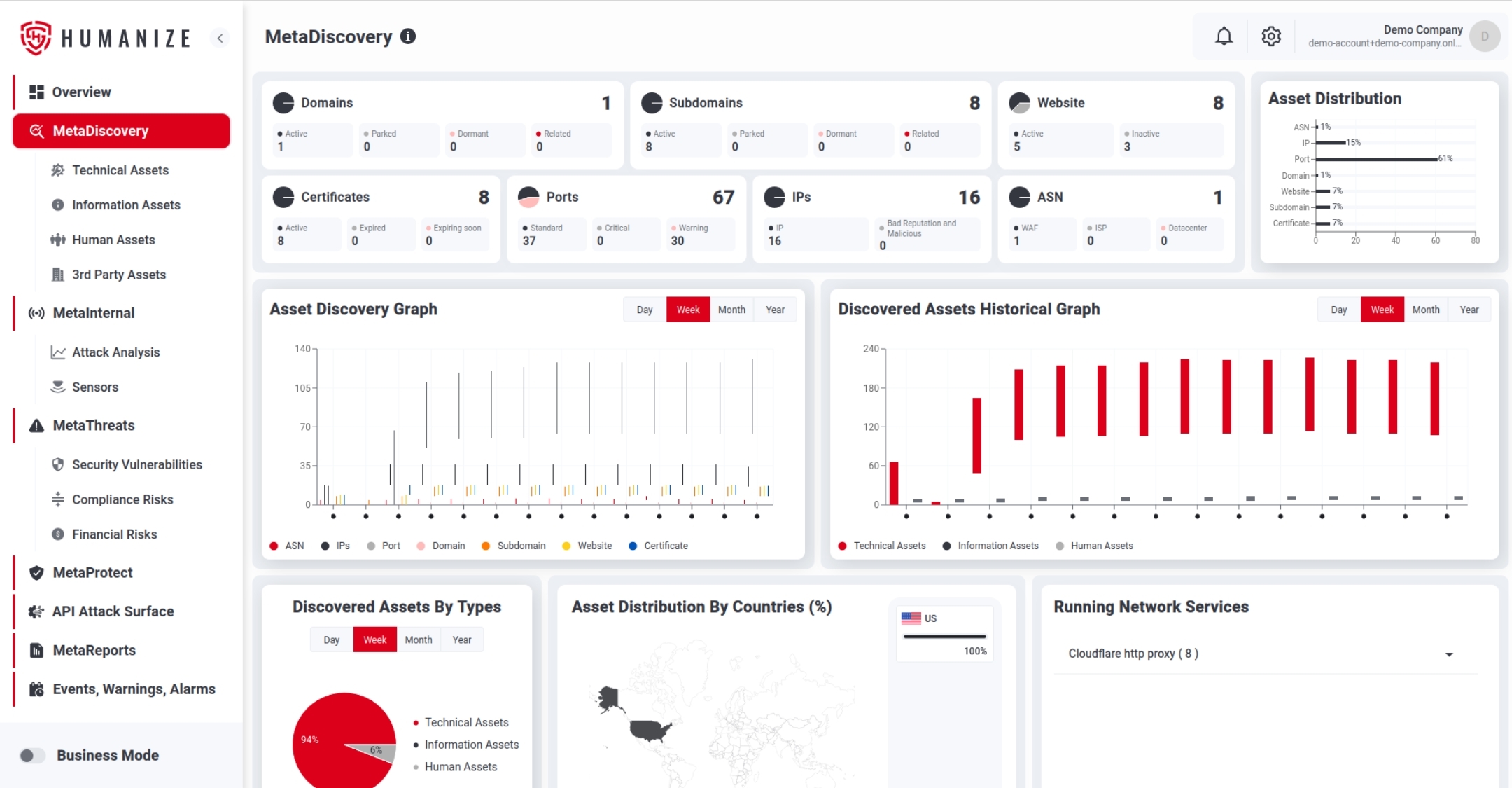
Broad asset visibility across your entire external ecosystem
Active and passive checks to confirm vulnerabilities, misconfigurations and exposure
Automatically leverage discovery techniques and enrich assets
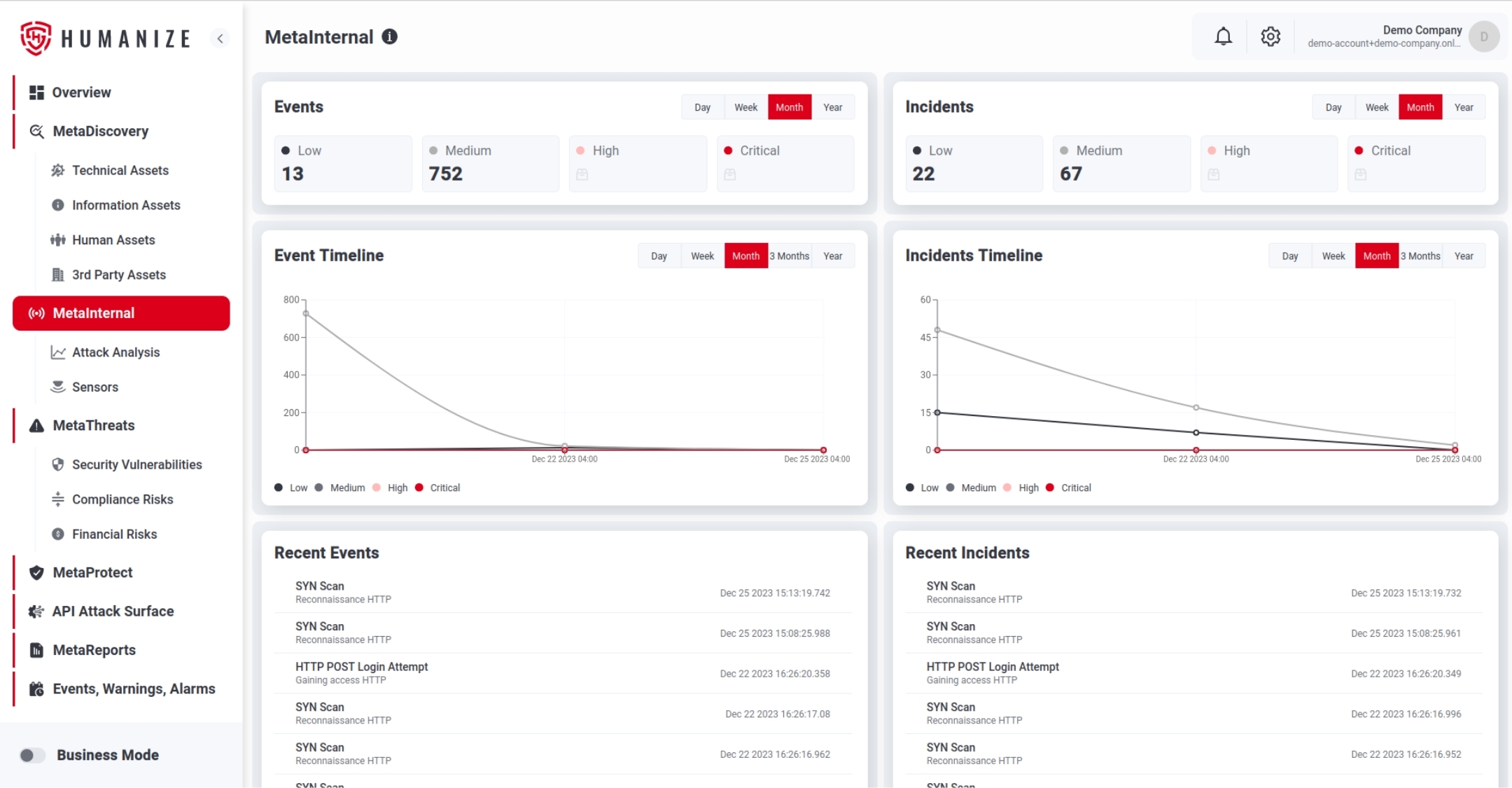
The process of analyzing the security misconfigurations, weaknesses and vulnerabilities.
A security event of higher priority that requires attention for the action in a short-term period.
The process of translating the number and report data into useful recommendations and guidelines for the managers and C-Suite.
The technical, human, and informational assets of the partner companies are in any type of business relations that contribute to creating a business value of the company.
Utilize Salience's risk measurement to simplify budget allocation and assess your cybersecurity ROI.
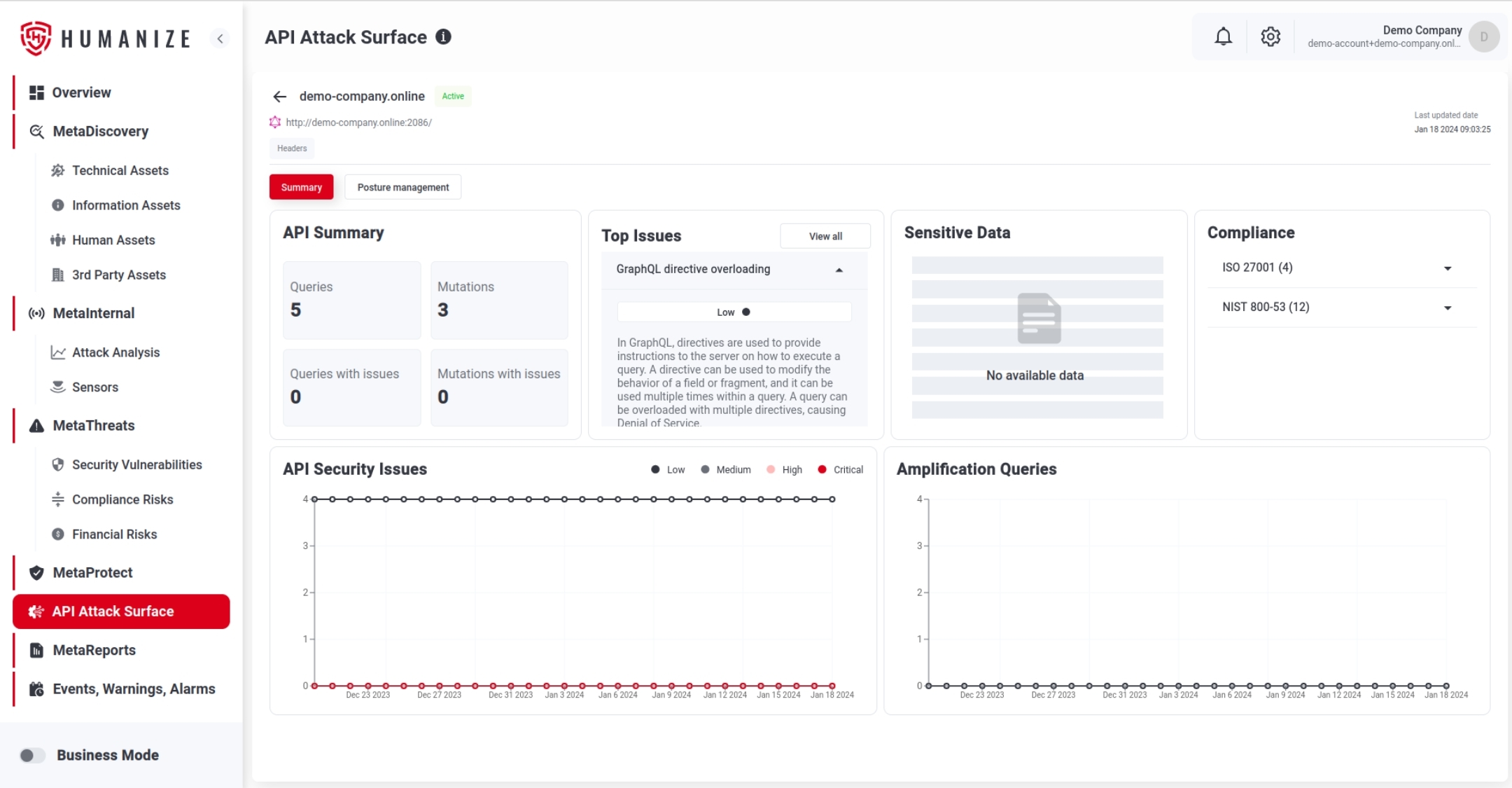
Enhance your API security by addressing vulnerabilities and misconfigurations while simplifying secure API deployment through Salience's continuous analysis.
Gain a complete view of your entire attack surface, covering external, internal, and API assets.
Leverage Salience's intelligent honeypot techniques and attacker tactic.
Our cybersecurity platform uses automated penetration testing methods and tools to detect weaknesses, misconfigurations, and vulnerabilities within your IT systems and networks.
